The Corellium Resource Library
The latest articles and news on mobile app security testing, IoT and research from Corellium and community contributors.
Corellium •
May 16, 2024
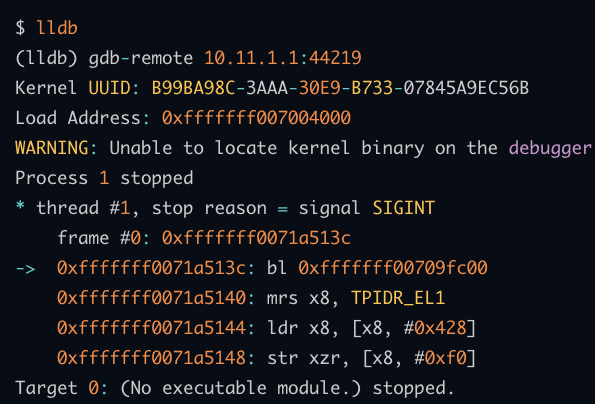
How to Debug the Kernel
Corellium virtual devices allow you to inspect and modify the state of the whole system under user control. Discover how in this kernel debugging how to guide.
Corellium •
May 16, 2024
Accessing Kernel and Physical RAM from Userland
Discover how Corellium virtual devices enable access to kernel or physical views of VM RAM.
Corellium •
May 16, 2024
Using Root from Apps
Discover how to use su from an app you're installing on a Corellium device.
Corellium •
May 16, 2024
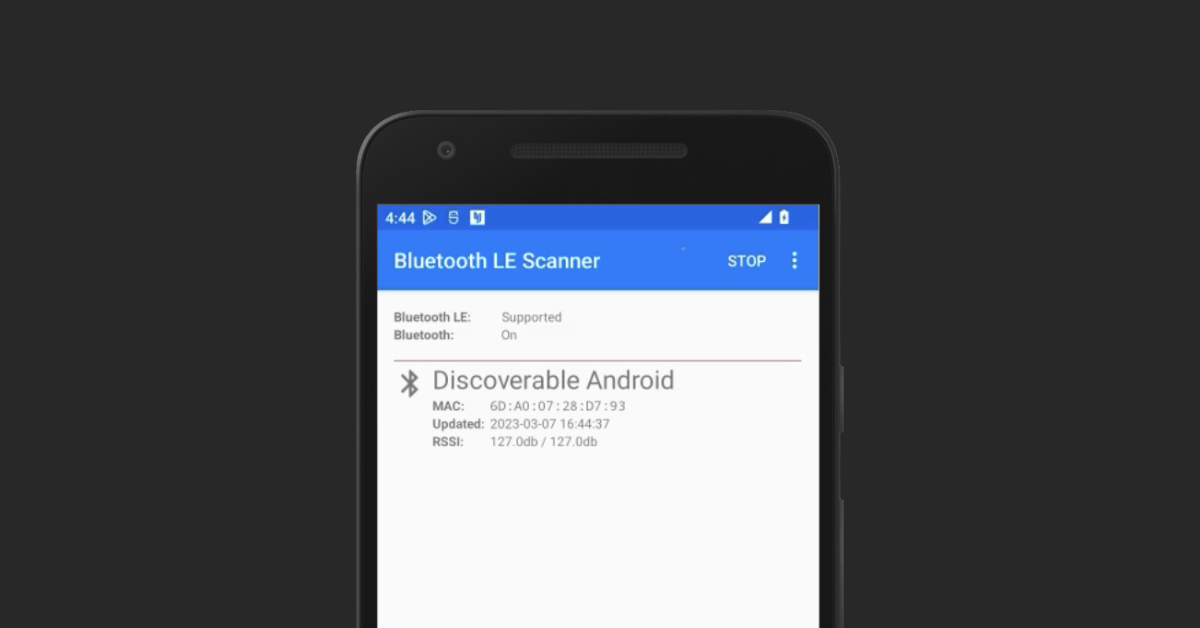
Demonstrate a Bluetooth Connection
Discover how to configure two virtual Android devices in order to demonstrate a working Bluetooth connection on Corellium.

Bill Neifert •
May 15, 2024
Accelerating Software Development for Next-Generation Arm-based Automotive Solutions
Corellium hypervisor technology, powering Arm-based virtual platforms, can enable accelerated, scalable, and agile software development in automotive. Watch how.
Corellium •
May 09, 2024
How to Debug Userland Native Code
Debugging Userland native code can be frustrating. This step-by-step guide will help you untangle the complexities.
Corellium •
May 09, 2024
Build a Custom Kernel for Android on Debian-based Linux
Want to build a custom Android kernel? It's easier than you think! Learn how with this step-by-step guide.

Steven Smiley & Brian Robison •
May 09, 2024
Mobile Vulnerabilities Exposed: Data at Rest
Learn about exposing mobile app vulnerabilities in data at rest. Watch our expert webinar or read the recap and case study.
Steven Smiley & Brian Robison •
Apr 30, 2024
Mobile Vulnerabilities Exposed: Data in Transit
Learn how to capture network traffic and protect data in transit. Watch our expert webinar or read the recap and case study.

Corellium •
Apr 26, 2024
Deep Dive into Experimenting with Messaging App Vulnerabilities
Marco Chomut of TFP0 Labs dives deep into experimenting with messaging app vulnerabilities in our latest webinar. Watch today.
Bill Neifert •
Mar 14, 2024
Introducing the Cortex-R82AE and Cortex-R82 System Models
Arm unveils next-gen automotive IP for software-defined vehicles and emphasizes software flows leveraging virtual hardware platforms. Discover how our solutions are key to these cutting-edge developments.

Chris Williams •
Feb 29, 2024
Introducing MicroSnapshots - Leveraging copy-on-write memory
Join Corellium for a demo showcasing our MicroSnapshots feature, designed for rapid restoration of a virtual machine's state, ideal for snapshot fuzzing.
Subscribe to Stay Connected
Keep up to date with emails for the latest product news and technical articles.
