Technical Articles
The latest technical articles and news on mobile app security testing, IoT and research from Corellium and community contributors.

Steven Smiley •
May 26, 2023
iOS Database Storage with Corellium
When conducting a mobile app security assessment, testing iOS database storage is critical. Learn how to test iOS app data storage in the DVIA-2 application.

David Manouchehri •
May 05, 2023
Routing Real SMS Messages from Twilio to Corellium via Cloudflare Workers
Learn how to use Corellium, Cloudflare workers, and Twilio to build an SMS handling system for mobile security purposes. Code samples and screenshots are included.

David Manouchehri •
May 03, 2023
Leveraging Corellium and Cloudflare Workers for iOS Virtual Device Management
The need for quality iOS emulators continues to rise. Learn how to use Corellium with Cloudflare workers to make iOS virtual device management simple and scalable.
Brian Robison •
Apr 28, 2023
3 Mobile App Security Testing Challenges and How to Overcome Them
Mobile app security testing is full of tedious tasks, but it’s vital to find vulnerabilities before bad actors do. Read about challenges and how to overcome them.

David Manouchehri •
Apr 14, 2023
The Calls Are Coming from Inside the House
Learn how to set up SSH reverse tunneling in the Corellium app to help you with investigating phishing attacks on iOS. Code and rationale is provided.

Steven Smiley & Brian Robison •
Apr 04, 2023
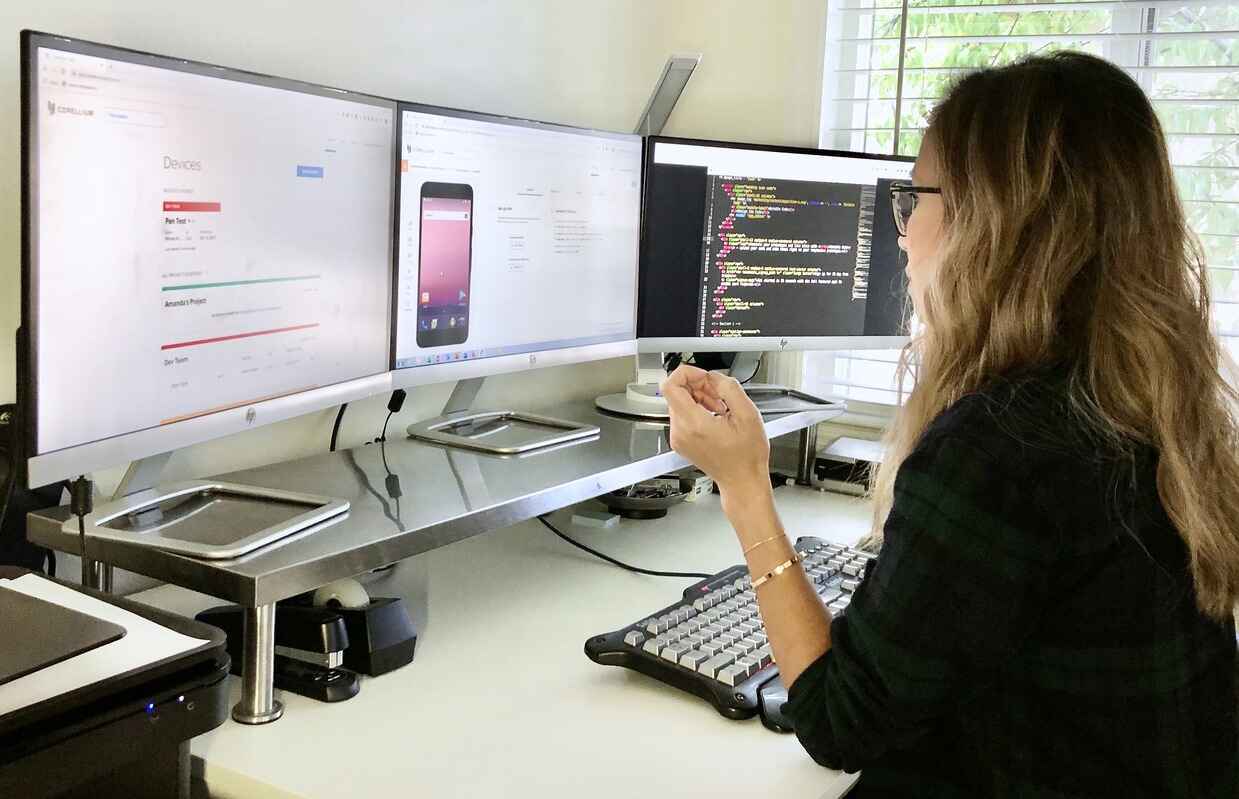
Mobile Vulnerabilities Exposed: Change What's Possible in Mobile App Security Testing
Physical devices are tedious to manage and device emulation is insufficient. Learn a better way to conduct mobile app security testing with Arm virtualization.

David Manouchehri •
Mar 10, 2023
Creating a Safe Browsing, Serverless API to scan iOS apps with Corellium & Frida on AWS Lambda
Learn how to create a serverless Safe Browsing API that actually works for iOS apps to scan for security issues using Corellium, Python, and Frida on AWS Lambda.

Steven Smiley •
Jan 05, 2023
Intro to iOS mobile reverse engineering
Learn how to reverse engineer an app: tools, applications, and analysis for dissecting iOS applications effectively.

Steven Smiley •
Nov 30, 2022
Understanding SSL Certificate Pinning: Boost Mobile Security with Corellium
What is SSL certificate pinning and how is it implemented for iOS and Android?

Steven Smiley •
Oct 26, 2022
Exploiting Android local storage with Corellium
How to examine, detect and exploit sensitive information being stored by an Android application

Steven Smiley •
Oct 20, 2022
Exploiting iOS local storage with Corellium
How to examine, detect and exploit sensitive information being stored by an iOS application

Alex Hude •
Oct 12, 2022
Behind the scenes: Using Corellium to build Corellium models
An example of how we used our Corellium platform to debug one of our virtual iPhone models
Subscribe to Stay Connected
Keep up to date with emails for the latest product news and technical articles.
